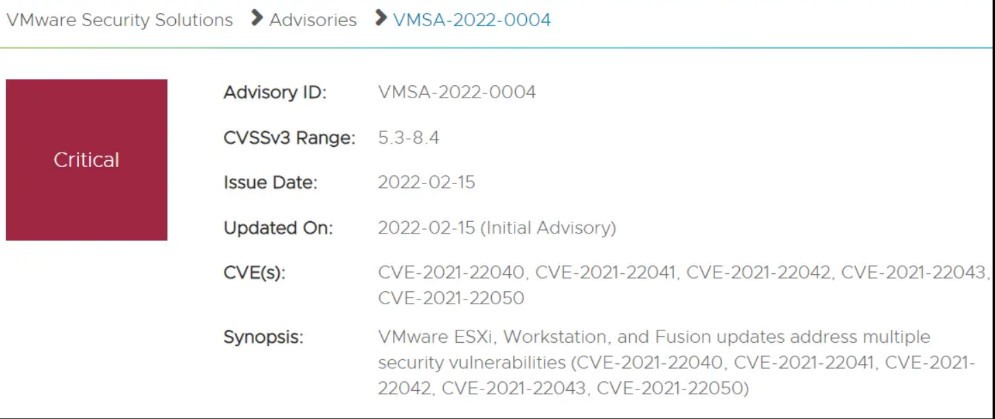
VMware 发布了一份安全公告 VMSA-2022-0004,提供了针对中国天府杯期间发现的影响 VMware ESXi、Workstation、Fusion 和 Cloud Foundation 的多个漏洞的补丁程序。公告涵盖了 CVE-2021-22040、CVE-2021-22041、CVE-2021-22042、CVE-2021-22043 和 CVE-2021-22050。
VMware has issued a security advisory VMSA-2022-0004, providing patches for multiple vulnerabilities discovered during the China Tianfu Cup affecting VMware ESXi, Workstation, Fusion and Cloud Foundation. The bulletin covers CVE-2021-22040, CVE-2021-22041, CVE-2021-22042, CVE-2021-22043, and CVE-2021-22050.
VMware, for its part, encourages customers to deploy its products "in a security-hardened configuration," applying all updates, security patches, and mitigations.
VMware ESXi, Workstation and Fusion contain a use-after-free vulnerability in the XHCI USB controller. VMware has assessed the severity of this issue in the Important severity range, with a CVSSv3 base score of up to 8.4. And VMware ESXi, Workstation and Fusion contain a double-fetch vulnerability in UHCI USB controllers. The severity assessment is also in the Important severity range, and the highest CVSSv3 base score is also 8.4. Both issues could be exploited by malicious actors with local administrative rights on the virtual machine to execute code as the virtual machine's VMX process running on the host.
VMware said ESXi contains an unauthorized access vulnerability because VMX has access to settingsd authorization tickets. It gave the issue a maximum CVSSv3 base score of 8.2, and noted that a hacker with privileges in the VMX process might only be able to access the settings service running as a privileged user.
VMware ESXi also has a TOCTOU (Time-of-check Time-of-use) vulnerability in the way temporary files are handled; the highest CVSSv3 base score is also 8.2, as it allows a malicious actor with settingsd access to write Arbitrary files to escalate privileges.
ESXi contains a slow HTTP POST denial of service vulnerability in rhttpproxy. VMware has rated this issue as moderate severity with a maximum CVSSv3 base score of 5.3. A malicious actor with access to the ESXi network could exploit this issue to create a denial-of-service condition with multiple requests overwhelming the rhttpproxy service.
While VMware urges users to apply all patches, the bulletin also states that removing the USB controller from the virtual machine may help resolve the issue. The move may not be feasible at scale, though, and "won't eliminate potential threats like patching."
"The consequences of this vulnerability are severe, especially if an attacker could gain access to workloads in your environment. Organizations that practice change management using ITIL change type definitions would consider this an emergency change."
For details, please check the official announcement
VMware 方面鼓励客户“以安全强化配置”部署其产品,同时应用所有的更新、安全补丁和缓解措施。
VMware ESXi、Workstation 和 Fusion 在 XHCI USB 控制器中包含一个 use-after-free 漏洞。VMware 已评估此问题的严重性在 Important severity range,CVSSv3 基础得分最高为 8.4。且 VMware ESXi、Workstation 和 Fusion 在 UHCI USB 控制器包含一个 double-fetch 漏洞。严重性评估也在 Important severity range,CVSSv3 基础得分最高同样也为8.4。在虚拟机上拥有本地管理权限的恶意行为者都可能利用这两个问题,以在主机上运行的虚拟机 VMX 进程的身份执行代码。
VMware 表示,由于 VMX 有权访问 settingsd authorization tickets,因此 ESXi 包含未经授权的访问漏洞。它给该问题的最高 CVSSv3 基础评分为 8.2,并指出在 VMX 进程中拥有权限的黑客可能只能访问作为高权限用户身份运行的设置服务。
VMware ESXi 还存在一个 TOCTOU(Time-of-check Time-of-use)漏洞,存在于处理临时文件的方式中;最高 CVSSv3 基础得分也是 8.2,因为它允许具有 settingsd 访问权限的恶意行为者可以通过编写任意文件来提升权限。
ESXi 在 rhttpproxy 中包含一个缓慢的 HTTP POST 拒绝服务漏洞。VMware 已评估此问题的严重性在中等严重程度,最高 CVSSv3 基础得分为 5.3。具有 ESXi 网络访问权限的恶意行为者可能会利用这个问题,通过使用多个请求 overwhelming rhttpproxy 服务来创建一个 denial-of-service 条件。
虽然 VMware 敦促用户应用所有补丁,但公告也指出,从虚拟机中移除 USB 控制器可能有助于解决这个问题。不过此举在规模上或许是不可行的,并且“不会像打补丁那样消除潜在威胁”。
“这个漏洞的后果是严重的,特别是如果攻击者可以访问你环境中的工作负载。使用 ITIL 变更类型定义来实践变更管理的组织会认为这是一种 emergency change”。
详情可查看官方公告
