Apache Log4j2引发严重安全漏洞,疑似很多公司的服务器被扫描攻击,一大批安全人员深夜修bug,堪称“核弹级”漏洞。
经专家研判,该漏洞影响范围极大,且利用方式十分简单,攻击者仅需向目标输入一段代码,不需要用户执行任何多余操作即可触发该漏洞,使攻击者可以远程控制用户受害者服务器,90%以上基于java开发的应用平台都会受到影响。
12月9日晚,对很多程序员来说可能是一个不眠之夜。12 月 10 日凌晨,Apache 开源项目 Log4j 的远程代码执行漏洞细节被公开,由于 Log4j 的广泛使用,该漏洞一旦被攻击者利用会造成严重危害。
据悉,Apache Log4j 2.x <= 2.14.1 版本均回会受到影响。根据“ 微步在线研究响应中心 ”消息,可能的受影响应用包括但不限于:Spring-Boot-strater-log4j2、Apache Struts2、Apache Solr、Apache Flink、Apache Druid、Elasticsearch、Flume、Dubbo、Redis、Logstash、Kafka 等。很多互联网企业都连夜做了应急措施。
截至本文发出,斗鱼、京东、网易、深信服和汽车产业安全应急响应中心皆发文表示,鉴于该漏洞影响范围比较大,业务自查及升级修复需要一定时间,暂不接收 Log4j2 相关的远程代码执行漏洞。
Apache Log4j2 caused serious security vulnerabilities. It is suspected that many companies' servers were scanned and attacked. A large number of security personnel repaired bugs late at night, which can be called "nuclear bomb level" vulnerabilities.
Experts have determined that the scope of the vulnerability is extremely large, and the method of exploitation is very simple. The attacker only needs to enter a piece of code into the target, and the user does not need to perform any redundant operations to trigger the vulnerability, allowing the attacker to remotely control the user's victim server , More than 90% of application platforms developed based on java will be affected.
The evening of December 9th may be a sleepless night for many programmers. In the early morning of December 10, the details of the remote code execution vulnerability of the Apache open source project Log4j were made public. Due to the widespread use of Log4j, the vulnerability would cause serious harm once it is exploited by attackers.
It is reported that Apache Log4j 2.x <= 2.14.1 will be affected. According to the "Weibu Online Research Response Center" message, possible affected applications include but are not limited to: Spring-Boot-strater-log4j2, Apache Struts2, Apache Solr, Apache Flink, Apache Druid, Elasticsearch, Flume, Dubbo, Redis, Logstash , Kafka, etc. Many Internet companies have taken emergency measures overnight.
As of this article, Douyu, JD, NetEase, Sangfor, and the Automotive Industry Safety Emergency Response Center have all issued documents stating that given the relatively large scope of the vulnerability, business self-examination and upgrade and repair will take a certain period of time, and remote code execution related to Log4j2 will not be accepted for the time being Loopholes.
1 The vulnerability caused by the lookup function Log4j is an open source Java logging tool. Logging is mainly used to monitor the changes of variables in the code, and periodically record them in files for other applications to perform statistical analysis; track the trajectory of the code when it is running, as the basis for future audits; act as a debugger in the integrated development environment , To print the debugging information of the code to the file or the console. Therefore, for programmers, logging is very important.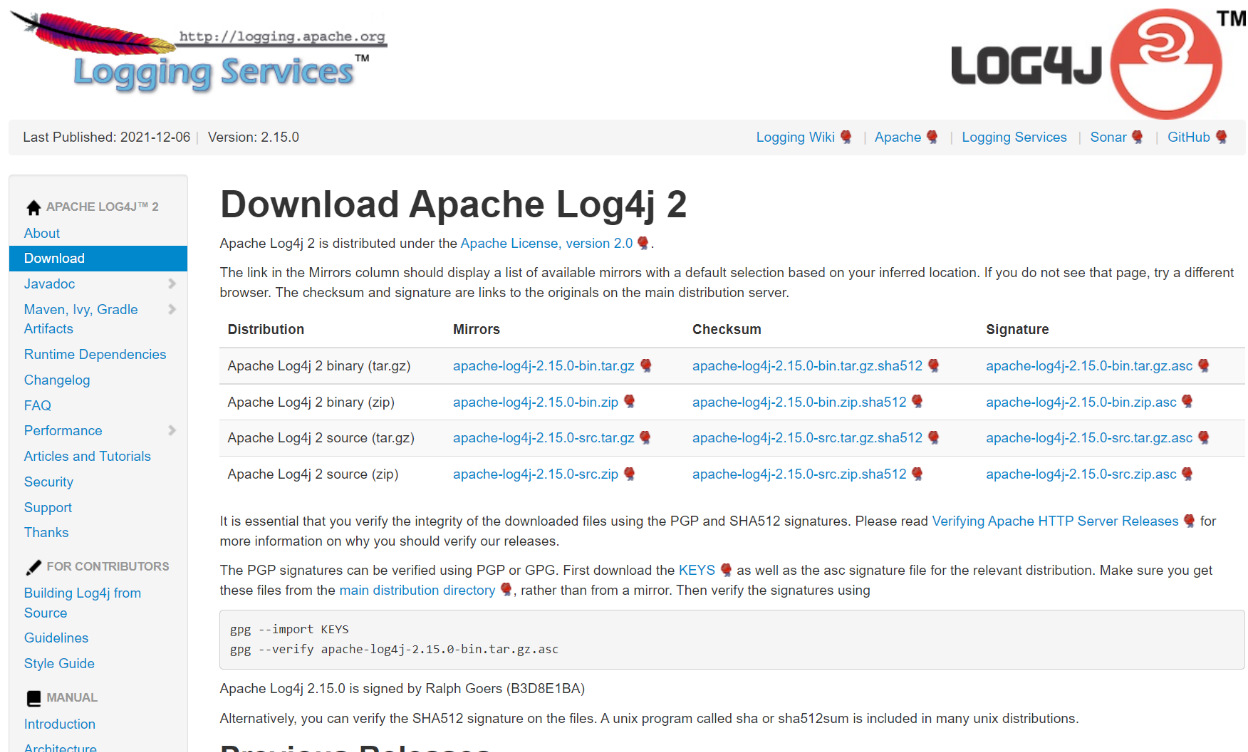
Today, with emphasis on the development of reusable components, Apache provides a powerful log operation package Log4j. Log4j can easily control whether log information is displayed, the type of log information output terminal, output mode, output format, and more detailed control of the log generation process, and it can be configured flexibly through configuration files without requiring a lot of code changes. Therefore, many Internet companies choose to use Log4j.
In 2014, Log4j 2 was released. Log4j 2 is a major upgrade to Log4j, completely rewriting the log implementation of log4j. Log4j 2 provides many improvements available in Logback, while fixing some inherent problems in the Logback architecture. It has been updated to version 2.15.0.
Log4j2 also supports SLF4J, which can automatically reload the log configuration and supports advanced filtering options. In addition, it allows delayed evaluation of log statements based on lambda expressions, provides asynchronous loggers for low-latency systems, and provides a garbage-free mode to avoid any delays caused by garbage collector operations. Through other language interfaces, companies can also use Log4j in C, C++, .Net, and PL/SQL programs.
The emergence of this vulnerability is caused by the lookup function provided by Log4j 2, which allows developers to read the configuration in the corresponding environment through some protocols. However, in the process of implementation, no strict judgment was made on the input, which caused loopholes. The "Microstep Online Research Response Center" has reproduced the vulnerability: Simply put, when printing the log, if the keyword ${ is found in the log content, then the content contained in the log will be used as a variable to replace it, leading to an attack The person can execute commands arbitrarily. Detailed vulnerability disclosure can be viewed at: https://issues.apache.org/jira/projects/LOG4J2/issues/LOG4J2-3201?filter=allissues Any data from online web services may be written to Log4j, even some pre-auth For example, registration and login, the actual attack entry depends on the specific situation of the business. At present, Baidu search, Apple iCloud search, 360 search, etc. all have this problem.
Picture source: public account "Road to Confidence"
On the morning of December 10, the Alibaba Cloud security team issued a warning again and found that Apache Log4j 2.15.0-rc1 had a vulnerability bypass. It is recommended to update to Apache Log4j 2.15.0-rc2 in time.
Regarding this vulnerability, some netizens commented, "It can be said that it is a catastrophic vulnerability, which is more serious than the previous fastjson and shiro. It is estimated that this vulnerability will continue to exist in the next three or four years..."
2 Rapid detection and repair plan In response to this vulnerability, the "Weibu Online Research and Response Center" also gave some emergency plans.
1. Emergency mitigation measures (1) Modify the jvm parameter -Dlog4j2.formatMsgNoLookups=true (2) Modify the configuration log4j2.formatMsgNoLookups=True (3) Set the system environment variable FORMAT_MESSAGES_PATTERN_DISABLE_LOOKUPS to true 2. Detect plan 3. Repair plan to check that all Log4j is used The official repair link of the component system is as follows: https://github.com/apache/logging-log4j2/releases/tag/log4j-2.15.0-rc13 Security should be an ongoing process. Everyone knows the importance of security. However, security issues still occur frequently.
In May last year, 360 Cyber Security Response Center issued the "Fastjson Remote Code Execution Vulnerability Notice". The announcement stated that the Java library fastjson <= 1.2.68 version has a remote code execution vulnerability, and the vulnerability can be exploited to directly obtain server permissions. The vulnerability was assessed as a "high-risk vulnerability" and its impact was "widely."
A year ago, the Alibaba Cloud Emergency Response Center monitored that Apach Shiro officially disclosed a vulnerability in its cookie persistence parameter rememberMe encryption algorithm. Attackers can use the Padding Oracle attack method to construct a malicious rememberMe value, bypass encryption algorithm verification, and perform java reverse sequence Operationalization can eventually lead to remote command execution to obtain server permissions, which is extremely risky.
Security itself is not a function that can create value, but more like a function that needs to consume value to ensure functional stability. Small and medium-sized enterprises often do not have enough funds to invest in safety construction, and enterprises with funds will also minimize this part of the budget.
It is difficult to estimate the likelihood of successful cyber attacks and the extent of potential losses. Decision makers usually rely on empirical judgments to decide the amount of investment. According to Alex Blau's article in the Harvard Business Review, decision makers have three misunderstandings when making a decision: Treat cyber security as a defense. In this process, powerful firewalls and capable engineers can keep them away from threats.
Think that it is safe enough to comply with security frameworks such as NIST or FISMA.
I thought that if there were no security vulnerabilities in the near future, then the parts that seemed to have no problems would not need to be repaired.
The problem with these ideas is that network security is not about solving limited problems, but should be an ongoing process. Erik Brynjolfsson, director of MIT's Digital Economy Initiative, said that combating cyber threats should be classified as a "higher priority." He believes that some repairs are not complicated. Although adding some additional small operations will make the entire process longer and increase a little cost, it will make enterprises and individuals safer.
Brynjolfsson pointed out that in terms of network security, the use of publicly available cryptography is usually more secure than proprietary systems built for specific companies.
The chief engineer of Oracle resigned angrily: MySQL is a "super bad database", it is recommended to consider a great failure in the history of PostgreSQL computer architecture, most people do not know that Didi launched the US stock delisting; Alibaba stock price fell back to 2017; Linus Tucao desktop version Linux: Randomly changed the core, the program compatibility is too bad | Q News This important open source project is maintained by a low-key "weird old man"! He propped up the computer world like Bill Gates. log4j is an open source project of Apache, a logging framework based on Java. Log4j2 is the successor of log4j, which is widely used in business system development and recording log information. Many Internet companies and well-known companies' systems are using this framework.
According to a netizen's description: "Baidu's homepage search was hacked, and all Java students got up to fix bugs, which had a great impact."
The remote code execution vulnerability in Log4j2 has been exploited by attackers and spread publicly. Trigger condition: As long as the data input by the external user will be recorded in the log, it can cause remote code execution.
Some netizens said: "It can be said that it is a catastrophic vulnerability, which is more serious than the previous fastjson and shiro. It is estimated that this vulnerability will continue to exist in the next three to four years."
If it is attacked, the scope of the impact will be comparable to that of the "Eternal Blue" virus in 2017. The WannaCry ransomware virus that year caused 300,000 users in at least 150 countries such as the United States, the United Kingdom, Russia, and China to be recruited.
Leifeng.com (public account: Leifeng.com) learned from Qi’anxin Group that, according to the monitoring data of Anyu Cloud Protection, as of 12 noon on December 10, nearly 10,000 attacks using this vulnerability have been discovered. Qi'anxin Emergency Response Center has received more than a dozen vulnerability emergency response requests from important units, and reported the vulnerability information to relevant authorities on the evening of December 9. According to the person in charge of the patching vulnerability response platform, in the middle of the night on December 9, more than 100 pieces of information about the vulnerability were submitted by white hat hackers in just one hour.
Security experts also said that open source software security governance is a long way to go, and requires the country, industry, users, and software vendors to pay attention and invest in order to achieve good results.
Flanker, a genius hacker and former Pinduoduo security expert, also stated on Weibo: "The vulnerability is serious. It is recommended to check all system dependencies and upgrade to log4j-2.15.0-rc1. The business system may not be directly quoted, but the bypassed log, Data and other Java system ecosystems are basically there, and they will still be beaten. "Urgent! Log4j vulnerability risk, comparable to "Eternal Blue" or will affect more than 70% of enterprises. According to Leifeng.com, on November 24, 2021, the Alibaba Cloud security team officially reported the Apache Log4j2 remote code execution vulnerability to Apache.
Yesterday, the Alibaba Cloud Emergency Response Center reminded users to take security measures as soon as possible to prevent vulnerability attacks, and said: Apache Struts2, Apache Solr, Apache Druid, Apache Flink, etc. are all affected.
Some manufacturers provide a troubleshooting method, and users only need to check whether the Java application has introduced two jars, log4j-api and log4j-core. If there is application usage, it is likely to be affected.
It seems that there is no unified solution yet. Some people in the industry said that they are waiting for the official patch, and choose to roll back the version for insurance. Looking at the current discussion situation, it is expected that the impact of the vulnerability will continue to ferment. ...
1lookup 功能造成的漏洞
Log4j 是一款开源 Java 日志记录工具。日志记录主要用来监视代码中变量的变化情况,周期性的记录到文件中供其他应用进行统计分析工作;跟踪代码运行时轨迹,作为日后审计的依据;担当集成开发环境中的调试器的作用,向文件或控制台打印代码的调试信息。因此,对于程序员来说,日志记录非常重要。
在强调可重用组件开发的今天,Apache 提供的强有力的日志操作包 Log4j。Log4j 可以轻松控制 log 信息是否显示、log 信息的输出端类型、输出方式、输出格式,更加细致地控制日志的生成过程,而其通过配置文件可以灵活地进行配置而不需要大量的更改代码。因此,很多互联网企业都选择使用 Log4j 。
2014 年,Log4j 2 发布。Log4j 2 是对 Log4j 的重大升级,完全重写了 log4j 的日志实现。Log4j 2 提供了 Logback 中可用的许多改进,同时修复了 Logback 架构中的一些固有问题,目前已经更新到 2.15.0 版本。
Log4j2 也支持 SLF4J,可以自动重新加载日志配置,并支持高级过滤选项。此外它还允许基于 lambda 表达式对日志语句进行延迟评估,为低延迟系统提供异步记录器,并提供无垃圾模式以避免由垃圾收集器操作引起的任何延迟。通过其他语言接口,企业也可以在 C、C++、.Net、PL/SQL 程序中使用 Log4j。
此次漏洞的出现,正是由用于 Log4j 2 提供的 lookup 功能造成的,该功能允许开发者通过一些协议去读取相应环境中的配置。但在实现的过程中,并未对输入进行严格的判断,从而造成漏洞的发生。“微步在线研究响应中心”做了漏洞复现:
简单来说,就是在打印日志时,如果发现日志内容中包含关键词 ${,那么这个里面包含的内容会当做变量来进行替换,导致攻击者可以任意执行命令。详细漏洞披露可查看: https://issues.apache.org/jira/projects/LOG4J2/issues/LOG4J2-3201?filter=allissues
由于线上 web 业务的任何数据都可能写入 Log4j,甚至一些 pre-auth 的地方,比如注册、登录,实际攻击入口取决于业务具体情况。目前百度搜索、苹果 iCloud 搜索、360 搜索等都出现了该问题。
图源:公众号“信安之路”
12 月 10 日上午, 阿里云安全团队 再次发出预警,发现 Apache Log4j 2.15.0-rc1 版本存在漏洞绕过,建议及时更新至 Apache Log4j 2.15.0-rc2 版本。
对于这次漏洞,有网友评价说道,“可以说是灾难性的漏洞,比之前的 fastjson 和 shiro 还要严重,这个漏洞估计在之后三四年内还会继续存在….”
2快速检测及修复方案
针对此次漏洞,“微步在线研究响应中心”也给出了一些应急方案。
1. 紧急缓解措施
(1)修改 jvm 参数 -Dlog4j2.formatMsgNoLookups=true
(2)修改配置 log4j2.formatMsgNoLookups=True
(3)将系统环境变量 FORMAT_MESSAGES_PATTERN_DISABLE_LOOKUPS 设置为 true
2. 检测方案
3. 修复方案
检查所有使用了 Log4j 组件的系统,官方修复链接如下: https://github.com/apache/logging-log4j2/releases/tag/log4j-2.15.0-rc1
3安全应该是一个持续的过程
每个人都知道安全的重要性,但安全问题还是频繁发生。
去年 5 月,360 网络安全响应中心发布“ Fastjson 远程代码执行漏洞通告”。通告称,Java 库 fastjson <= 1.2.68 版本存在远程代码执行漏洞,漏洞被利用可直接获取服务器权限。该漏洞评定为“高危漏洞”,影响面“广泛”。
前年,阿里云应急响应中心监测到,Apach Shiro 官方披露了其 cookie 持久化参数 rememberMe 加密算法存在漏洞,攻击者利用 Padding Oracle 攻击手段可构造恶意的 rememberMe 值,绕过加密算法验证,执行 java 反序列化操作,最终可导致远程命令执行获取服务器权限,风险极大。
安全本身并不是一个能够创造价值的功能,反而更像是需要消耗价值以确保功能稳定的功能。中小企业常常没有足够的资金投入安全建设,而有资金的企业也会把这部分预算将到最低。
网络攻击成功的可能性以及潜在损失的程度是难以实现估计的,决策者通常是依靠经验判断来做决定投入金额。根据 Alex Blau 在哈佛商业评论中的文章中提到的,决策者在作出决定时,会有一下三个误区:
将网络安全视为一种防御。在这个过程中,强大的防火墙和有能力的工程师可以让他们远离威胁。
认为遵守 NIST 或 FISMA 等安全框架就足够安全。
以为如果近期没有发生安全漏洞,那么看起来没有问题的部分就不需要修复。
这些想法的问题在于,网络安全不是要解决有限的问题,而应该是一个持续进行的过程。麻省理工学院数字经济倡议主任 Erik Brynjolfsson 表示,对抗网络威胁应该被归到“更高级别的优先考虑项”。他认为,一些修复并不复杂。虽然增加一些额外的小操作会让整个流程变长,并增加一点成本,但会让企业和个人更加安全。
Brynjolfsson 提出,在网络安全方面,使用公开可用的密码学通常比为特定公司构建的专有系统更加安全。
离职 Oracle 首席工程师怒喷:MySQL 是“超烂的数据库”,建议考虑 PostgreSQL 计算机架构史上的一次伟大失败,多数人都不知道 滴滴启动美股退市;阿里股价跌回2017年;Linus吐槽桌面版Linux:乱改核心,程序兼容性太糟糕 | Q资讯
这个重要开源项目全靠一位低调的“怪老头”维护!他和比尔盖茨一样撑起了计算机世界
log4j是Apache的一个开源项目, 是一个基于Java的日志记录框架。Log4j2是log4j的后继者,被大量用于业务系统开发,记录日志信息。很多互联网公司以及耳熟能详的公司的系统都在使用该框架。
据网友描述:“百度的主页搜索被黑了,所有Java同学起床修bug,影响很大”。
Apache Log4j 2.15.0 正式版地址 看第二页!
- 内容分页 1 2
