移动光猫G-140W-MD破解超级密码教程,兼讨论移动宽带没有公网IP,网心云端口限制型怎样修改映射公网型?
其实是问题比较多 老家里给老人开通了移动宽带,寻思上个网心云跑跑带宽,谁知上来就是端口映射型,按照目前自己的经验,先是路由器设置upnp,dmz 其实都不行,因为没有桥接,再加上开通了iptv 如果说改了桥接 ,很大可能电视看不成,因为电视iptv都是运营商自己内部协议,获取到的ip都是内网,桥接肯定不行‘**********************************************************************************************************************************目前,需要修改的东西顺序》》》》》》》》》》》》》》》》》》》》》》》》》》》》》》》》》》》》》》》》》》》》》》》》》》1.获取了光猫的超级密码才能修改猫内的upnp及dmz设置,看过下面的破解教程,很大概率会遇到各种问题,加上过年回家短短几天,一旦变砖搞坏,维修师傅都无法上门,风险较大,成功率较低,放弃
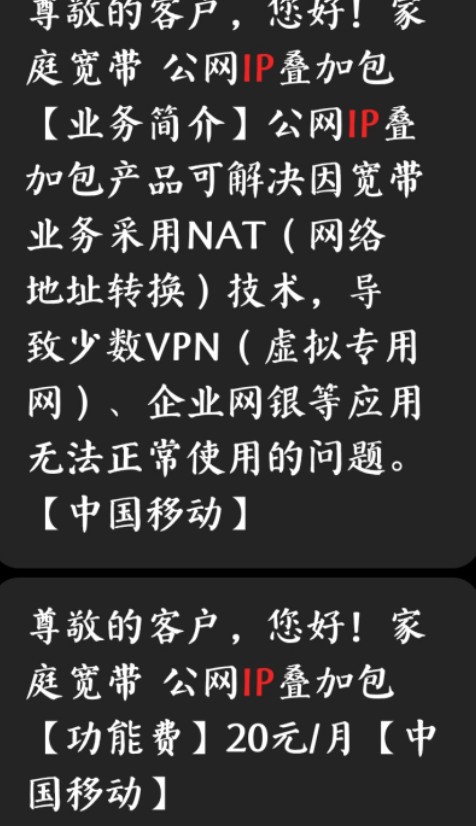
2.修改了桥接才能获取公网ip,用路由器的upnp功能及dmz设置,较大概率改了桥接,电视iptv无法使用,这个方案也只能放弃,通过找了几篇文章,大都是说移动无公网ip,需要买一个公网包才行,这方案也大概率要放弃。
这两种方案都放弃基本上就搞不了了,那些网心云里移动高收益要么是专线要么极客改的比较好,过年时间太短了,家里老人能看个电视就行了 ,不折腾了 下面是教程 供参考》》》》》》》》》》》》》》》》》》》》》》》》》》》》》》》》》》》》》》》》》》》》》》》》》》综上所述 ,这是一篇标题党 压根解决不了任何问题,正是如此,我吧折腾了大半天的成果在这里记录,供需要的人参考,其实还有一种解决办法,就是改桥接,然后自己去买个电视盒子,申请移动公网ip,这样既能挂网心云 又能看电视 就完美了 就这样本文完完全手打原创
Mobile optical cat g-140w-md super password cracking tutorial, and also discusses how to modify the mapping public network type when mobile broadband has no public network IP and netheart cloud port restriction type?
In fact, there are a lot of problems. My hometown has opened mobile broadband for the elderly. I think about the running bandwidth of netheart cloud. Who knows, it is port mapping. According to my current experience, first set UPnP on the router, but DMZ can't, because there is no bridge, and IPTV is opened. If the bridge is changed, I may not be able to watch TV, Because TV IPTV is the internal protocol of the operator, and the obtained IP is the intranet, the bridging is definitely not possible, Order of things to be modified 1 After obtaining the super password of Guangmao, you can modify the UPnP and DMZ settings in the cat. After reading the following cracking tutorial, you are likely to encounter various problems. In addition, in just a few days after returning home for the Chinese new year, once the brick is broken, the maintenance master can't come to the door, which is risky and has a low success rate. Give up
2. The public network IP can only be obtained by modifying the bridge. Using the UPnP function and DMZ setting of the router, the bridge is changed with a high probability, and the TV IPTV cannot be used. This scheme can only be abandoned. After looking for several articles, it is mostly said that there is no public network IP for mobile, so you need to buy a public network package. This scheme is also likely to be abandoned.
If you give up these two schemes, you can't basically do it. The high-yield mobile in the netheart cloud is either a dedicated line or a geek. The Chinese New Year is too short. The elderly at home can watch TV, Don't bother. The following is a tutorial for reference. To sum up, this is a title. The party can't solve any problems at all. That's right. I've recorded the results of tossing for most of the day here for reference, In fact, there is another solution, that is to change the bridge, and then buy a TV box and apply for mobile public network IP. In this way, it is perfect that you can not only hang the netheart cloud but also watch TV. In this way, this article is completely original
...
移动贝尔G-140W-MD破解超级密码教程
(photos of this model, with 2.4gwifi, but without external antenna, the signal strength is very weak)
==
A new mobile broadband is pulled. The default configuration issued by mobile is the routing mode, and changing the bridge requires a super password. When asking the broadband brother for the super password, they said they didn't know about the super password at all, so they had to crack it by themselves,
Baidu came back and found that no one else had shared the cracking tutorial of 140w-md (mobile customization),
The cracking method of bell 140W series customized by China Telecom Unicom is not applicable to mobile. After groping for a whole afternoon, we finally found the cracking method. So far, we share it in the jar for your reference.
==
The security of the mobile cat is very strict. The general cracking schemes commonly used for other models have been blocked: 1. Log in to the user account, backup the configuration file and view the password
2: User account login, web open telnet
(if the user accesses the hidden page, he will be automatically logged out and logged in!)
3: Chrome F12 tool to view super password
4: TTL (you're right, TTL Dharma can't handle it!)
(the show MDM command in the TTL terminal has been castrated)
==
But I finally found a way to crack it, that is, stabbing! Chrysanthemum! flower
Let's start the tutorial:
First, connect the network cable directly to the computer, enter 192.168.1.1, and log in with the user account password on the back of the cat,
Find the important configuration in the asterisk below and back it up elsewhere! In order to avoid being unable to automatically distribute the configuration, resulting in being unable to access the Internet!
Password: ***** (Mobile's optical authentication password, corresponding to China Unicom's loid)
INTERNET_*_ VID_** (VLAN ID number of Internet access)
VOICE_*_ VID_* (voice authentication configuration and password)
Other_*_ VID_* (IPTV parameters)
(since the landlord didn't handle IPTV and fixed line, I'm empty here. Please use the content that Baidu needs to back up for these two parameters)
Your broadband account
Your broadband password
After the backup is completed, the power on is in normal online state, and the optical fiber is directly unplugged! (if not, it will automatically restore the configuration)
Press and hold the reset hole on the back with a sharp object for more than 10 seconds until it restarts automatically!
After waiting for two minutes to reset, open 192.168.1.1 again,
Log in with the following default password:
Account No.: cmccadmin
Password: adm8h% MDA
Individual regions may be:
Account No.: admin
Password: cmcc10086#
After successful login, access this address in the address bar and click to start telnet:
http://192.168.1.1/system.cgi?telnet
Then go back to the background home page after super password login,
Enter the network, find the password authentication in the remote management menu, fill in the password you just backed up, and click apply.
Next, plug in the optical fiber and return to the background home page. If there is no problem, the configuration will be automatically distributed:
Wait for about 3 minutes. After the distribution is completed, the optical cat will restart automatically,
At this time, the super password will be modified due to automatic data distribution, but we have just started the telnet service,
Telnet will not be shut down due to automatic distribution, so you can start the next normal cracking steps!
==
The remaining steps can be directly referred to the post of the jar next door: a record of the success of cracking g140w-me super secret under telnet
Finally, I found that my super password was changed to cmccadmin + 8-digit random number
PS: note that after cracking, it is recommended to delete TR069 and turn off automatic reporting to avoid changing the super secret again!
...
(此型号的照片,带2.4Gwifi,但无外置天线,信号强度非常弱)
==
新拉了条移动的宽带,移动默认下发的配置是路由模式,而改桥接需要超级密码,在向宽带小哥问超级密码的时候他们表示完全不知道超密这回事,没办法只好自己动手破解了,
一圈百度回来发现140W-MD(移动定制)这个型号并没有其他人分享过破解教程,
电信联通定制贝尔140W系列的破解方式也并不适用于移动这个,摸索一下午之后终于找到破解方法,至此分享至坛子里供各位参考。
==
移动这个猫的安全做得相当狠,一般用于其他型号的通用破解方案都已经被堵死了:1:user账户登录,备份配置文件查看密码
2:user账户登录,web打开telnet
(user用户下访问隐藏页面会被自动注销登录!)
3:chrome F12工具查看超级密码
4:ttl(对你没看错,ttl大法都搞不定它!)
(ttl终端中的show mdm命令已经被阉割)
==
不过最终还是被我找到了破解方法,那就是捅!菊!花!
下面开始教程:
首先网线直接连接电脑,进入192.168.1.1,用光猫背面的user账户密码登录,
翻找下面的星号中的重要配置备份到其他地方!以免无法自动下发配置导致不能上网!
Password:*****(移动的光认证密码,对应电信联通的loid)
INTERNET_*_VID_**(上网的VLAN ID号)
VOICE_*_VID_*(语音鉴权配置和密码)
Other_*_VID_*(IPTV参数)
(由于楼主没办理iptv和固话,所以我这里是空的,这两个参数请自行百度需要备份的内容)
你的宽带账号
你的宽带密码
备份好之后,开机正常上网状态,直接拔掉光纤!(不这样操作它会自动还原配置)
用尖锐物品按住背面的复位孔十秒以上,直到自动重启!
等待两分钟重置完成之后再次打开192.168.1.1,
用下面的默认超密登录:
账号:CMCCAdmin
密码:aDm8H%MdA
个别地区可能是:
账号:admin
密码:Cmcc10086#
登录成功之后在地址栏访问这个地址,点击开启telnet:
http://192.168.1.1/system.cgi?telnet
然后回到超级密码登录后的后台主页,
进入网络,远程管理菜单里找到password认证,填入你刚才备份的password,点应用。
接下来插上光纤,回到后台主页,如果没问题的话就会开始自动下发配置:
等待3分钟左右,下发完成之后光猫会自动重启,
此时超级密码又会因自动下发数据而被修改,但我们刚才已经开启了telnet服务,
telnet也实测不会因自动下发而被关闭,就可以开始接下来的正常破解步骤了!
==
剩下的步骤直接参考隔壁坛子的帖子即可:Telnet下破解G140W-ME超密成功纪实
最终发现我这里的超级密码被修改为了cmccadmin+8位随机数字……
ps:注意破解完毕之后建议删除TR069和关闭自动上报,避免超密再次被改!
链接 https://www.right.com.cn/forum/thread-3452473-1-1.html
https://tieba.baidu.com/p/7166132277
https://tieba.baidu.com/p/7216916556
https://tieba.baidu.com/p/7379831344
